Security Operations
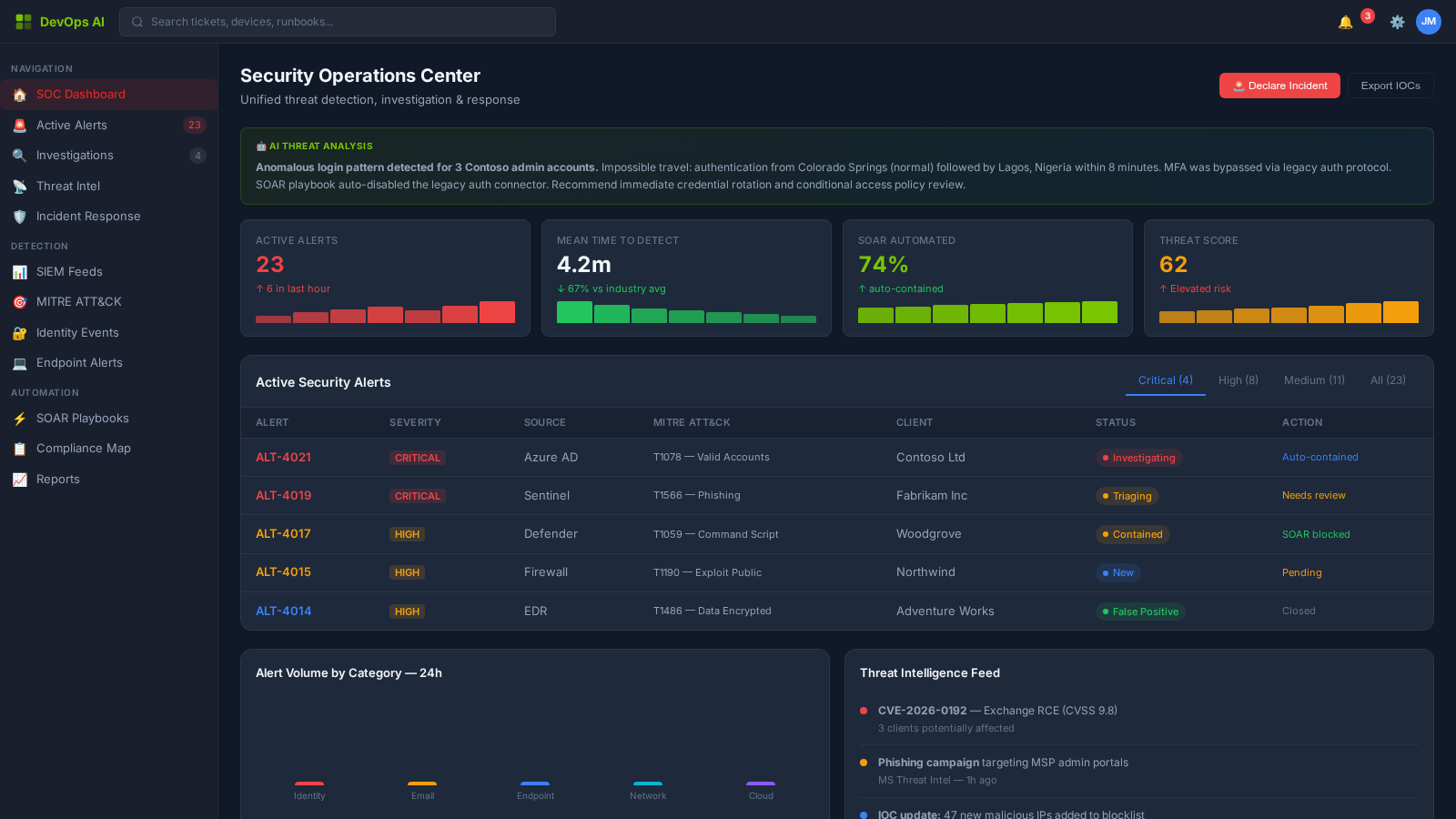
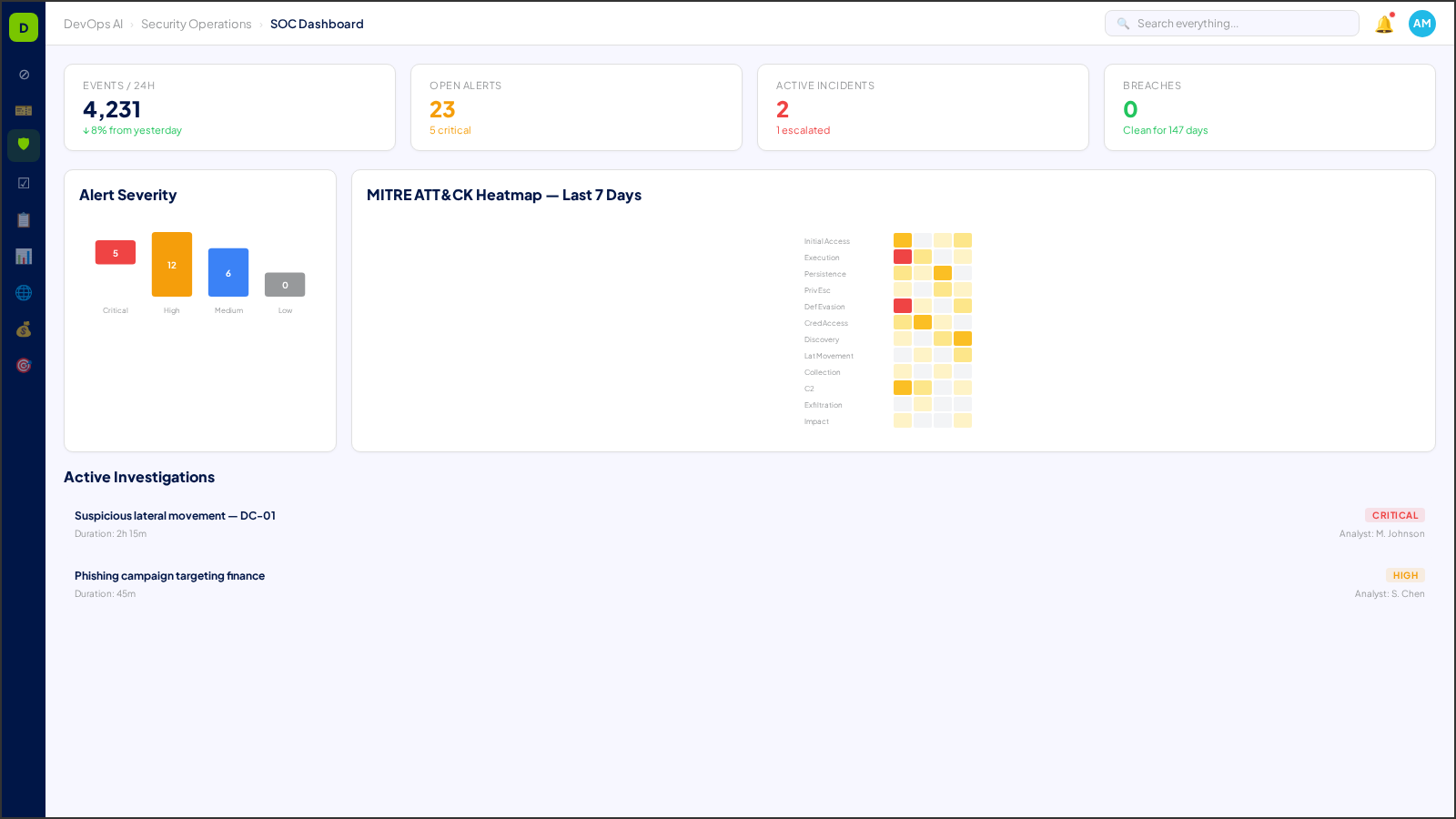
Unified SOC command center with AI-augmented threat detection, incident response, and zero-trust enforcement
Security Operations is the defensive nerve center of the platform. DevOps AI consolidates threat intelligence, incident response, vulnerability management, and privileged access into a single AI-augmented command center — reducing alert fatigue while ensuring no genuine threat goes unaddressed.
What You'll See
Real screens from the DevOps AI control plane — populated with representative data.
8 Process Areas
Each process area is classified with a Human-in-the-Loop (HITL) gate level — defining the boundary between AI autonomy and human oversight. Click any process area for a deep dive.
Incident Response Orchestration
L2 — Approve to ProceedAI-coordinated incident response with automated evidence collection, containment recommendations, and chain-of-custody documentation.
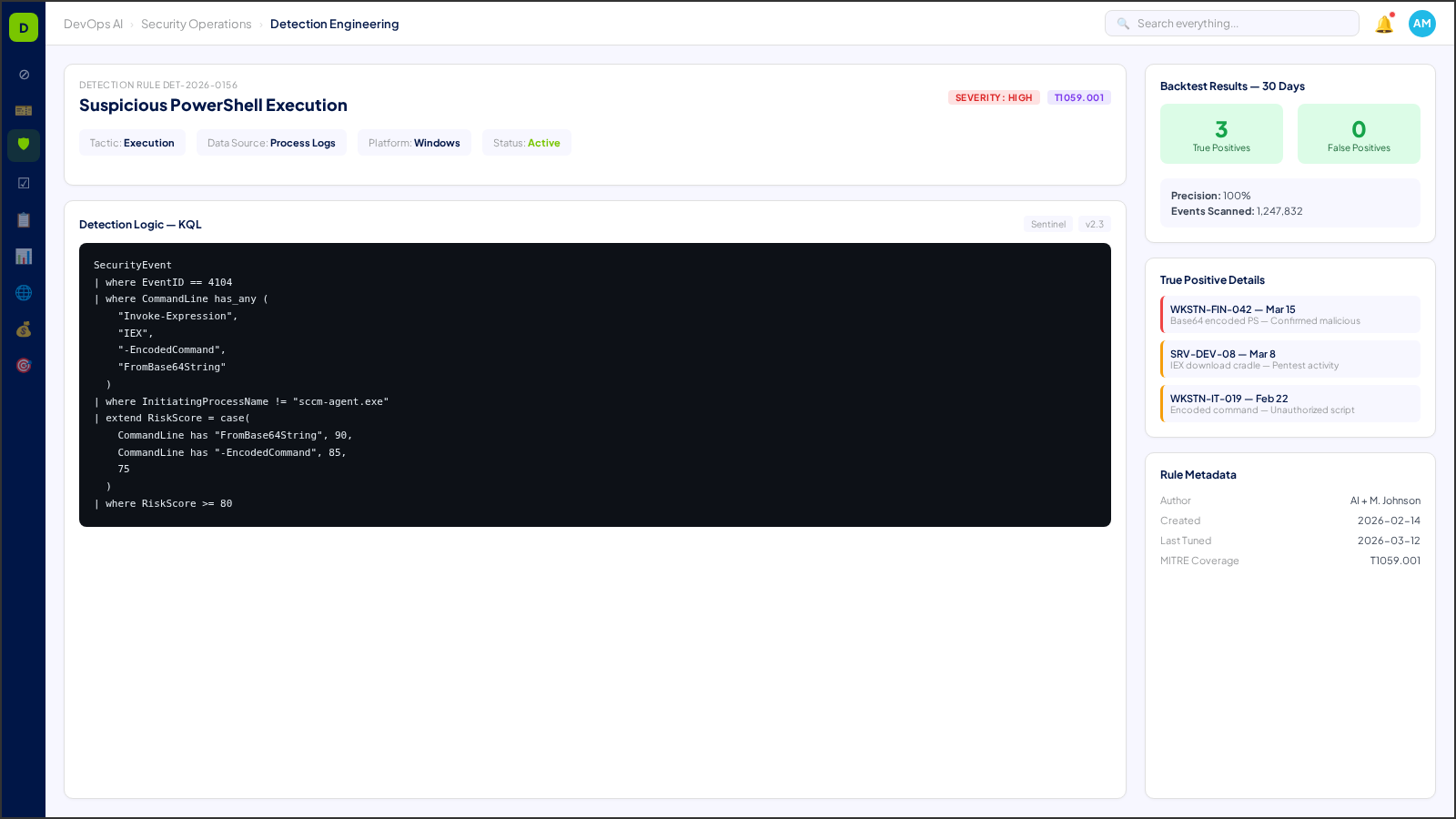
Deep Dive →Detection Engineering
L2 — Approve to ProceedCustom detection rules with AI-assisted tuning. Correlation engine maps alerts to MITRE ATT&CK techniques automatically.
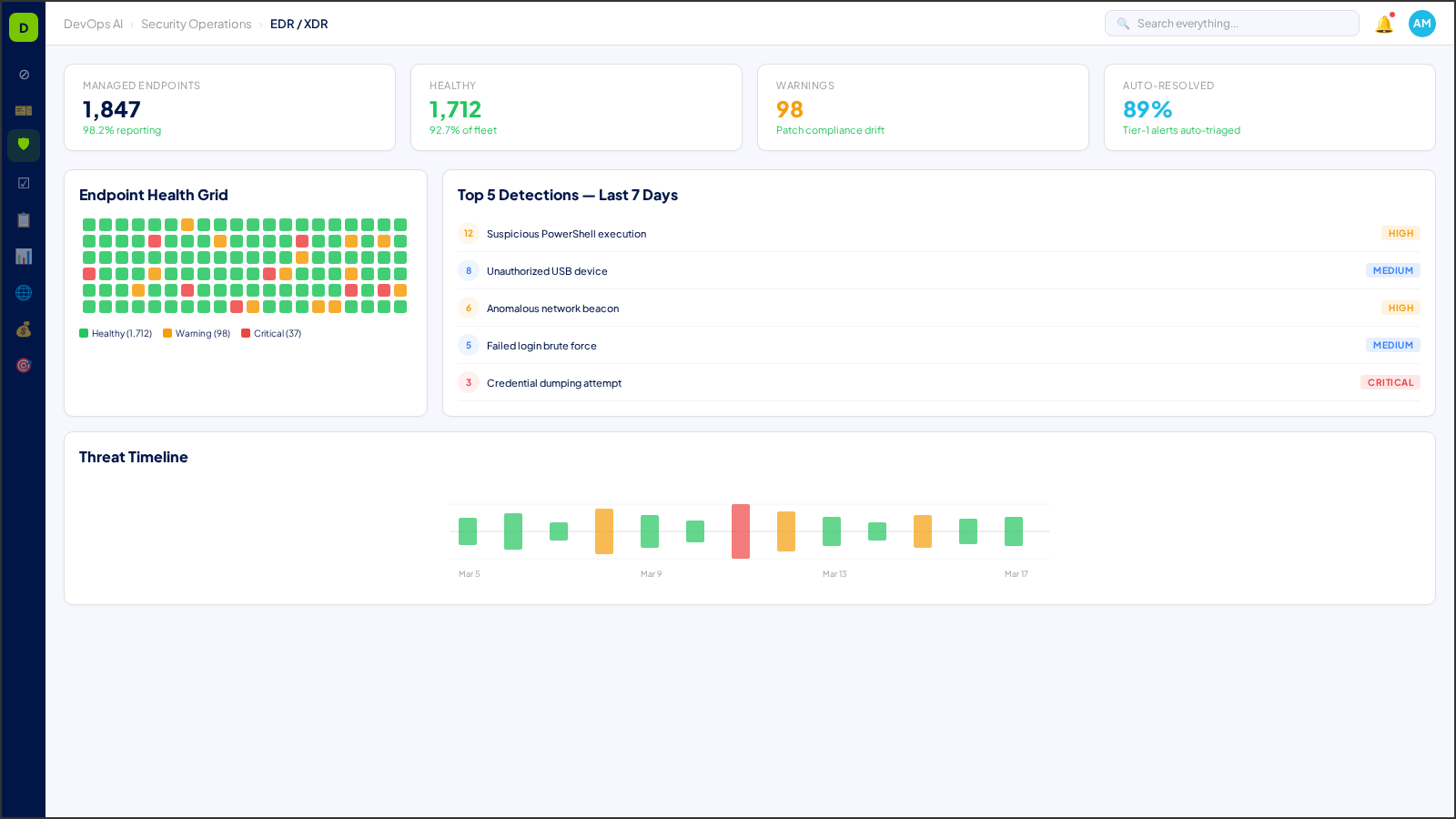
Deep Dive →EDR/XDR Integration
L1 — NotifyUnified endpoint detection across Wazuh, Defender, and third-party EDR platforms. AI triages 70-90% of Tier-1 alerts automatically.
Deep Dive →Zero-Knowledge Vault (ZK Vault)
L3 — Human OnlyClient-side encrypted credential storage. Secrets never leave the client's Azure tenant — the platform accesses credentials via ephemeral session tokens.
Deep Dive →Privileged Access Management (PAM)
L3 — Human OnlyJust-in-time access provisioning with full session recording. Every privileged action requires explicit approval and is logged immutably.
Deep Dive →Dark Web Monitoring
L1 — NotifyContinuous scanning of dark web sources for client credential leaks, domain mentions, and data exposure. Alerts with severity scoring.
Deep Dive →BCDR Planning & Testing
L2 — Approve to ProceedBusiness continuity and disaster recovery plans with automated testing schedules, RTO/RPO tracking, and failover documentation.
Deep Dive →Threat Intelligence Feeds
L0 — Fully AutomatedAggregated threat intelligence from multiple feeds with automated IOC enrichment and relevance scoring per client environment.
Deep Dive →Understanding HITL Gate Levels
Every process area in DevOps AI is classified by its Human-in-the-Loop (HITL) gate level — defining when AI acts autonomously and when human approval is required.
AI executes autonomously with full logging. No human approval needed. Examples: ticket classification, monitoring alerts, report generation.
AI executes and notifies the assigned human. Human can review, override, or escalate after the fact. Examples: SLA predictions, patch scheduling.
AI prepares and recommends, but a human must explicitly approve before execution. Examples: change requests, contract modifications, campaign launches.
Humans perform the action with AI providing decision support only. Examples: legal review, privileged access approval, incident legal response.
Who Uses Security Operations?
See how Security Operations transforms daily operations for these roles.
Works With
Security Operations integrates deeply with these operational zones.